ISO 27001 Information Security - Clause 5.2 Policy
17 May 2022 - ISO 27001 Information Security in plain English - Blog post #6.
A key element in demonstrating top management's leadership and commitment to Information Security is its Information Security Policy. This article discusses the requirements of Clause 5.2 Policy and how to address them.
ISO 27001 Information Security in plain English
Information Security is becoming critical to every business, and there is a fast-growing trend towards developing management systems based on the ISO 27001 standard. However, the subject and its terminology can certainly be a little daunting. So, we set out to cut through that in 'ISO 27001 Information Security in plain English' - a series of blogs articles that explains all clauses and controls in the standard.
Information security policy
One of the first steps in demonstrating top management's commitment to Information Security is to issue a statement of intent. That is known as an Information Security Policy, and such a document is a mandatory requirement of ISO 27001 (Clause 5.2 Policy). It should:
- Be appropriate to your organization and its mission.
That could (but doesn't have to) include a very brief summary of scope e.g. what you provide and where, and perhaps any over-arching ambition. - Provide a basis for your Information Security objectives.
You most likely would not list specific, individual objectives within the Information Security Policy, but perhaps state what type of subject matter you have objectives for. - State a commitment to satisfying requirements.
This would essentially be the chief executive's promise to comply with legal requirements, other compliance obligations, and other requirements. - State a commitment to continually improving your ISMS.
Once again, a promise to keep trying to do better.
The above is a minimum. Other inclusions may be added as per your preference. For example, you may choose to mention other voluntary commitments or assurances.
The Information Security Policy should be long enough to include the above elements without rambling on unnecessarily. In our view, a single page policy is most appropriate as it offers the best option for display and distribution purposes.
The policy should be authorised or signed off by the most senior person in the organization e.g. the Proprietor, Managing Director or C.E.O.
It is the responsibility of top management to ensure that the policy is known about, understood, and adhered to by people within the organization. There are plenty of low-cost ways of achieving that e.g. It may be included a newsletter, on an intranet, or even just talking about it at security awareness or team meetings.
There is also a requirement for the policy to be available to relevant interested parties. Apart from people that work for your organization, they might include a wide range of individuals and other organizations e.g. clients, shareholders, suppliers, regulatory bodies, or sources of funding for NGOs. A simple solution is to publish a copy of the policy on your web site.
Once the policy is established it also needs to be communicated to new workers that start subsequently. The ideal solution is to include ISMS or IMS awareness as part of the induction process. That should include making the policy available to them - perhaps by inclusion in an 'induction pack'.
The policy should be reviewed on a regular basis and updated as necessary. We would suggest that if there is a change of chief executive in the meantime, it should also be reviewed at that point and signed or re-authorised by that person.
Most ISO management system standards require just one formal policy document. However, in ISO 27001, the information security policy is just the over-arching policy document. There are also mandatory requirements for a number of additional policies. Templates for all of the required policies are available in ISO 27001 InfoSec Toolkit which is included in Qudos 3 IMS software. The toolkit also has a more detailed version of this article.
The previous blog post in this series is ISO 27001 Clause 5.1 Leadership and commitment.
The next blog in this series is on Clause 5.3 Organizational roles, responsibilities, and authorities.
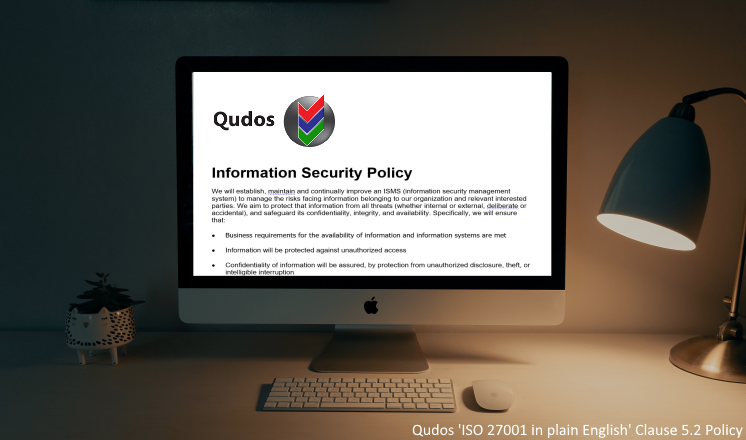
A template information security policy for you
To help you get started, here's a template information security policy. Just customise it to suit your own business needs.
It's an example of the many policies available in ISO 27001 InfoSec Toolkit which is included in Qudos 3 IMS software.
About the series 'ISO 27001 Information Security in plain English'
This blog post is part of a series where we will work through all the clauses and controls in ISO 27001. A great starting point for developing your ISMS.
This blog series began with an introductory webinar. A copy of the slide deck is available for you here:
Qudos_ISO_27001 Information_Security_in_plain_English (PDF)
Click the LinkedIn Follow button below to receive notifications.
There's nothing like word of mouth to share creative content. So, if you found this blog useful, please share it with a colleague or business associate.
Ready to start your journey to ISO 27001?
Qudos 3 IMS software includes an ISMS Overview template along with a wide range of tools to help you develop and maintain your management system faster, better and smarter.
The first step to commencing a management system based on ISO 27001 is to conduct a Gap Analysis. We can provide a qualified, experience certification auditor to perform a professional Gap Analysis service for you.
Contact us today to discuss your needs!
Image based on a photo by Clay Banks on Unsplash

